Everyone in the Account Is a Customer
Trust Buyers, Trust Personas, and the Hidden Gates of Enterprise Value
Note: this essay continues the line of thinking first introduced in “Hidden in Plain Sight” and “Leading the Pivot”
The Old Map Fails at the Gate
Most companies lose trust because their map of value motion is too small. They believe they understand the sale because they have named the budget holder, the champion, the user, the decision maker, and the person who feels the pain. That map works for a while. It works in the early conversation, inside the demo, during the first internal pitch, and through the moments where everyone is still talking about the widget. Then the deal reaches a gate the map never named. Security asks for more. Privacy wants a data boundary answer the team cannot produce cleanly. Legal inserts conditions. Procurement slows the process. Finance hesitates. A committee asks a question that never appeared in the sales plan. The revenue team calls these people “blockers” or “friction” because the revenue team has been trained to see them as such. That is the first category error.
“Everybody in the customer account is a customer. There is no such thing as an enemy in an account. There are only customers.”
I want to teach you to see the account differently. The person who slows the deal is often the person carrying the exposure that everyone else has ignored. The person asking for more proof may be the only person in the process who understands what will happen if the decision goes wrong. The person everyone wants to bulldoze may be the human being whose felt safety determines whether value can move. When I say that “everybody in the customer account is a customer,” I mean it literally. The CISO is a customer. Privacy counsel is a customer. Procurement is a customer. The integration lead is a customer. The board-facing risk operator is a customer. The compliance reviewer is a customer. The person with no budget, no enthusiasm for your product, and no interest in your feature set can still be the person who controls a value journey gate.
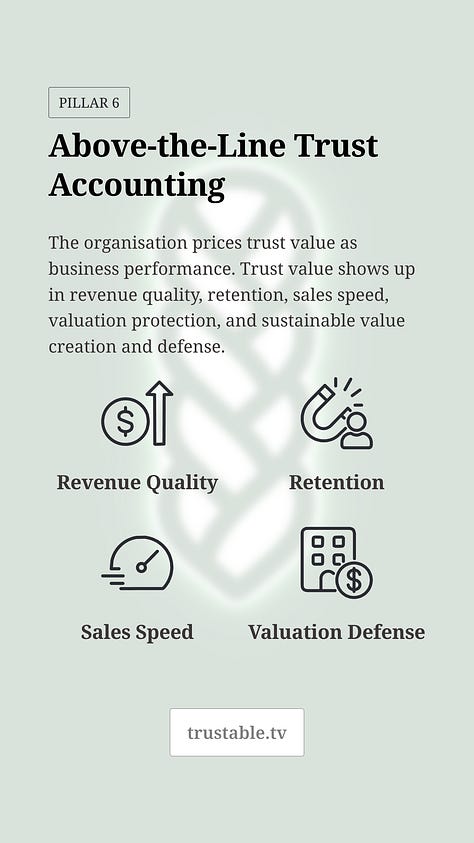
The old map teaches the business to hunt for budget. Trust Value Management teaches the business to map value exposure along a value journey’s path. Budget tells you who can pay, but exposure tells you who must carry consequence. Modern enterprise buying is a team sport because value rarely moves through one human being anymore. It moves through a sequence of gates, each with its own operator, its own burden, its own fear, its own threshold, its own incentives, its own consequence environment, and its own standard of proof. The buyer who signs the contract may want your widget, but the trust buyer at the gate may be asking a different question: is my value safest with you? That question is where this essay begins.
The Human Being at the Gate
A trust buyer is a stakeholder along the Value Journey who controls, borrows, or influences a decision gate. The phrase is simple because the object has to be teachable. It also carries a lot of machinery. A trust buyer may have no budget. They may never use the product. They may never meet the salesperson. They may have no aesthetic opinion about the thing being sold. They may care nothing about the pitch. Nonetheless, they still matter because value cannot move without their permission, and their permission is shaped by exposure.
“A trust buyer is a stakeholder along the Value Journey who guards a decision gate.”
Exposure means someone pays when the decision fails. Payment can mean legal liability, operational burden, reputational damage, career risk, political cost, lost confidence, delayed integration, internal rework, customer harm, board scrutiny, or the simple misery of becoming the person who has to explain why the wrong vendor was allowed through the gate. The trust buyer is the person who feels that possible payment. They are often the person who has to carry the decision after the sales team has celebrated the win. They are looking at your company through the question everyone else tries to avoid: when pressure arrives, will you preserve my value or externalize your pressure onto me?
This is how the “deal blocker” frame destroys value. Once the business labels a trust buyer as a blocker, it begins to treat the person as an obstacle to overcome rather than a buyer to serve. The sales organization tries to route around them. Product treats their requirements as backlog. Security treats them as auditors with paperwork appetites. Legal treats them as contract friction. Customer success hopes they disappear after close. The result is predictable. The gate operator senses contempt, missing proof, or evasive motion. The value gate hardens. Trust friction rises. Value slows, reprices, or dies.
I am not asking the business to be nicer to procurement because procurement people have feelings. I am saying procurement is buying a form of safety. Legal is buying a form of safety. Security is buying a form of safety. Privacy is buying a form of safety. Finance is buying a form of safety. They are all inside the account, and they are all judging whether your company can hold their organizational, professional, and tactical value without degradation, disruption, betrayal, or embarrassment. Each one of them buys a different form of that trust. Each one has a different exposure profile. Each one needs a different proof object.
A trust buyer guards a gate because, at that moment in the value journey, institutional permission runs through them. They may not own the whole decision, but they own enough of the clearance condition to matter. The gate may be security review, vendor approval, data access approval, legal posture settlement, procurement authorization, underwriting, board posture, investor diligence, renewal review, or incident response settlement. The name of the gate changes by industry and journey stage but the mechanism stays stable: value is exposed, a human being or institution must decide whether to allow value to move, and that decision requires felt safety under scrutiny.
The Trust Persona Planning Object
The trust buyer and the trust persona are two sides of the same coin: the trust buyer is the field actor while the trust persona is the internal planning object. The trust buyer appears as a person, role, committee, review lane, authority holder, or institutional checkpoint. The trust persona is what product, engineering, security, legal, marketing, revenue, customer success, and Trust Quality build around before the gate becomes trust friction.
“The security backlog exists because there is no economic buyer for “security” like there is for trust.”
This distinction matters because organizations plan around the people they know how to name. Product teams name users, so users get requirements. Revenue teams name economic buyers, so economic buyers get messaging. Customer success names champions, so champions get attention. Finance names budget holders, so budget holders get modelled. The hidden trust buyer appears late because nobody made them a first-class planning object and thus their requirements arrive as interruptions. The CISO wants proof of reliability under load. Privacy wants a map of data flow and responsibility boundaries. Legal wants bounded claims and recourse language. Procurement wants insurance, continuity, and substitutability. Integration wants technical clarity. The auditor wants evidence that the company will not become a governance problem. Because no persona existed for these people, the company experiences their needs as surprise or worse: trust friction.
The security backlog is the cleanest example. The security backlog exists because there is no economic buyer for “security” inside product or GTM planning. A security fix competes with a visible feature. Evidence generation competes with interface polish. Reliability work competes with near-term roadmap promises. Data boundary clarity competes with the cosmetic object that a product manager can point at in a release note. Product says it has to prioritize the user. Revenue says it needs the feature. Engineering says the backlog is already over capacity. Security says the work is critical. Everyone argues because the planning system lacks a complete view of all personas who receive value from the widget (not just the feature or economic buyer).
The trust persona changes the argument. It says there are people who may never use the product but require first-class consideration as if they were users, because their permission allows the product to sell, renew, integrate, expand, and be valued. If a trust buyer needs evidence of data boundary control, product has to expose or generate that evidence. If a trust buyer needs proof of security, engineering has to build the capabilities that make that proof real. If a trust buyer needs reliability under load, the roadmap must include the tests, telemetry, SLOs, rollback paths, and story-ready outputs that demonstrate Competency. The trust persona converts hidden gate pressure into planned work.
This is why trust personas cannot live inside marketing alone; they belong inside product requirements, engineering prioritization, security remediation, evidence production, Trust Quality certification, customer success cadences, legal posture, revenue enablement, and annual planning. The trust persona is someone you build for in product, someone you remediate for in engineering, someone you plan around in operating cadence, and someone marketing learns to speak to before sales needs them. Once that object exists, the organization stops treating trust work as compliance or backlog, and begins treating it as work that clears value gates.
Custody: Why Companies Exist
A company exists because someone gave it value to hold. That value may be money, data, operational dependency, personal information, attention, brand confidence, labor, regulatory permission, public legitimacy, or the customer’s ability to keep operating without fear. The company receives that value into custody. The better it holds that value, the more everyone can grow. The worse it holds that value, the more trust friction appears, the more cost the system pushes outward, and the more the company has to compensate with discounting, persuasion, legal force, speed, or noise.
“Safe motion means that humans are making decisions prioritizing the safety of the value that has been entrusted to our custody.”
This way of thinking is foreign to many operators because they have been trained to inhabit a model created somewhere else. A thesis arrives with metrics and priorities attached, and the operator is told what counts as value and what counts as cost. The company becomes a machine for executing the thesis, and every motion inside the machine is judged by the metrics embedded in that thesis. The operating reality narrows. The business stops asking how it actually makes money through all of its surfaces, and instead asks whether the sales number, product velocity number, efficiency number, or cost number fits the playbook criteria. Under that compression, enormous value surfaces disappear.
Safe human motion is the operational unit of custody. Every time a human being makes a decision, clicks a button, approves a request, changes a configuration, answers a customer, drafts a clause, ships a feature, closes a ticket, updates a policy, or decides to look away, motion happens. Some of that motion protects entrusted value. Some of it erodes trust value. Some of it creates a short-term gain by increasing future consequence. Some of it clears a gate or sets the organization up for future gate clearance. Some of it plants a landmine that revenue will step on next quarter. The trust question is whether that human motion advanced the Value Journey while preserving stakeholder value safety.
Unsafe motion often looks efficient in the moment. It moves the business from A to B faster, then leaves an explosion behind it. The company then has to outrun the explosion it created. It has to go faster to stay ahead of the consequence debt of its own shortcuts. That is how trust gets burned as fuel. The business celebrates velocity while the field fills with hidden trust friction. Later, the friction appears as delayed deals, legal concessions, customer hesitation, audit escalation, renewal anxiety, and valuation drag. Everyone is confused because the local metrics looked fine. The gate tells the truth. The field prints the cost.
Stakeholder Value Safety is the condition where stakeholders receive expected value without fear of degradation, disruption, or betrayal. That definition matters because it gives trust work a terminal condition. The stakeholder has to be able to settle into permission under scrutiny. They have to be able to say, without reservation, I can sign this, I can let this through. I can allow this vendor into the environment. I can accept this renewal. I can present this to the board. I can depend on this company without becoming the person who pays for their failure. The trust buyer is the human carrying that settlement burden.
Where Value Is Delayed, Repriced, Constrained, or Released
The Value Journey is the planning surface that lets the company see these trust gates before they become emergencies. It is a backwards planning model. You begin with the value state you want to achieve: a signed contract, an approved vendor, a cleared security review, a renewal without re-litigation, a successful expansion, a clean board posture, a stronger valuation, a lower diligence burden, or a customer who can continue without fear. Then you work backward. Which gates must clear? Who operates them? What exposure do they carry? What proof is sufficient? What story should reach them before the gate hardens? Which operational outputs must exist so the story is true?
“The Value Journey is a backwards planning model.”
The Value Journey prevents the company from treating customer, revenue, product, and valuation as separate worlds. They are separate sub-journeys, but they form one value motion surface. Revenue feels a deal stall in diligence. Product feels an unplanned requirement. Legal feels a contract escalation. Customer success feels renewal anxiety. Finance feels discounting or delayed cash. Valuation feels risk, legal burden, revenue timing uncertainty, loss volatility, and the market’s suspicion that the company cannot scale safely. These are often the same gate failure observed from different locations inside the business.
A decision gate is the atomic planning object. It should have an owner, a clearance criterion, an exposure description, a minimum evidence set, a sufficiency threshold, a refresh cadence, and links to the trust stories and certified artifacts that support it. A gate exists where a decision creates outsized consequence under scrutiny. Vendor approval is a gate. Security review is a gate. Legal posture settlement is a gate. Feature release is a gate. Data access approval is a gate. Underwriting is a gate. Investor diligence is a gate. Board posture is a gate. Each one asks the same operational question in a different accent: can the exposed party safely let this value move?
Trust friction is what happens when the answer is unstable. It appears as cycle time, rework, pricing pressure, legal concessions, engineering one-offs, repeated document requests, bespoke assurances, audit escalation, stalled procurement, customer hesitation, renewal drag, or sudden board attention. Trust friction is valuable because it prints the real requirements landscape. The company may believe its diligence documentation is complete, but the market may disagree. The company may believe its product is ready, but the trust buyer may feel exposed. The company may believe its controls are sufficient, but the gate may ask for a different form of proof.
A trust friction event should become a typed record: gate, stakeholder class, exposure condition, timestamp, stall mode, request payload, competitor delta, concession cost, internal rework cost, routing decision, certification dependency, story update trigger, and next review date. Without intake, every delayed deal becomes an anecdote. With intake, the trust value erosion pattern becomes visible. The same trust buyer appears repeatedly. The same evidence gap opens. The same gate fails. The same competitor creates contrast. The same internal team absorbs the same emergency. Once the pattern is visible, the business can build instead of improvising.
Trust Comes After Safety
One of the most important corrections in this work is that trust comes after safety. Companies ask to be trusted too early. They say, trust us, we have a SOC 2. Trust us, we have a policy. Trust us, we have a security team. Trust us, we have customers like you. Trust us, the contract says the right words. But the trust buyer does not want the word “trust” first. The trust buyer wants to know whether their exposed value is safe with you. Safety is demonstrated before trust is granted. Trust comes after the human has seen the choreography of safety in a form they can feel and inspect.
“Trust comes after safety. You have to prove that you are capable of safety by demonstrating the choreography of safety in a story.”
A Trust Story exists for that reason. It is a narrative sequence combining validated artifacts, context, affective resonance, and stakeholder incentive at a specific point in the Value Journey. It is narrated evidence in motion that tells the exposed human what value is at risk, how that value is protected, which mechanisms hold, where the boundaries are, how the claim is refreshed, what happens when conditions drift, and why the person can safely continue. The story organizes evidence so the human at the gate can settle into permission without doing all of the interpretive labor alone.
This is why ordinary compliance bundles often fail to clear gates. Everyone has a SOC 2. Everyone has a penetration test. Everyone has a certificate of insurance. Everyone has redacted policies. Everyone has a trust center. These things may be necessary today, but they rarely create advantage by themselves because they are baseline artifacts without gate-specific sufficiency. They are often correct and cold. They sit in a repository and wait for a stressed human to make meaning out of them. The trust buyer has seen too much of that. They are not waiting for another static pile of documents; they are waiting for someone to understand the exposure they carry.
The sale we make to the trust buyer is affective because the trust buyer is a human being. Paperwork creates feeling. Silence creates feeling. Delay creates feeling. Evasion creates feeling. A clean, bounded, well-sequenced proof object creates feeling. The business often pretends that legal, security, compliance, privacy, and procurement people are purely rational evaluators of facts, but frankly human beings do not work that way. They feel first and then decide whether the facts fit the field already formed. Trust Value Management respects the human-level nature at which gate permission actually occurs, and its first task of evidence is to create a field where the human can interpret safely.
The hidden trust buyer question is, is my value safest with you? The CISO asks that through operational dependency, incident response, access control, reliability, and blast radius. Legal asks it through liability, truthfulness, accountability, and enforceable boundaries. Privacy asks it through data movement, consent, purpose limitation, and disclosure posture. Procurement asks it through continuity, substitutability, financial stability, insurance, and vendor risk. Customer success asks it through renewal ease, support burden, and relationship continuity. The board asks it through governance, valuation susceptibility, and public consequence. Each role asks the same question through a different exposure surface.
Who Needs to Feel What?
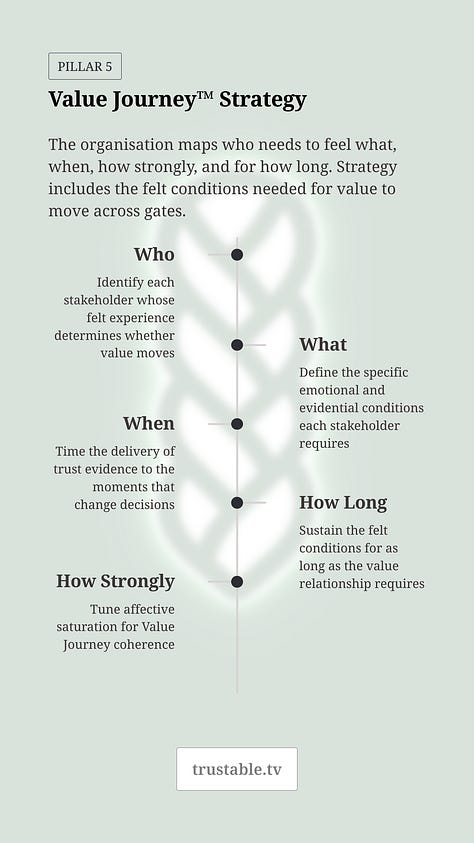
The central value journey planning question is: who needs to feel what, where in the Value Journey, at what point, for how long, and at what level of intensity? That question sounds simple because it has to be teachable. It is also the bridge between the Value Journey and 8CM. The Value Journey tells us where the gates are. Exposure tells us who pays if the decision fails. The trust buyer tells us who must settle into permission. 8CM tells us which felt trust constituents the proof must activate.
“Who needs to feel what, where in the Value Journey, at what point, for how long, at what level of intensity?”
The eight trust constituents are Clarity, Compassion, Character, Competency, Commitment, Consistency, Connection, and Contribution. Their anti-states are Confusion, Callousness, Corruption, Negligence, Abandonment, Inconsistency, Alienation, and Exploitation. These are the affective acceptance surface of trust. The trust buyer experiences evidence through these dimensions simultaneously, especially under exposure. A CISO facing operational dependency may need Competency, Commitment, Consistency, and Clarity. A legal reviewer facing liability may need Character and Clarity. A customer after an incident may need Compassion, Commitment, and Consistency. A board gate may need Character, Competency, evidence yield, and proof of governed change across time.
This is why the question cannot be reduced to what document do they want? A trust buyer who asks for a SOC 2 may really be asking for Competency, Consistency, and Character. A trust buyer who asks for an incident response plan may be asking for Commitment under pressure and Compassion after harm. A trust buyer who asks for data flow diagrams may be asking for Clarity about boundaries and accountability. A trust buyer who asks for executive attestation may be asking for Character under incentive. The request payload is visible, but the affective requirement is the thing we have to learn to read.
8CM gives the planning team a way to translate exposure into target vectors. Clarity means the person can build an accurate mental model of the system they are inside: obligations, interfaces, decision rights, enforcement, and recourse. Competency means the person expects safe and reliable execution under normal conditions and stress. Character means the system remains bound to its stated constraints under incentive, pressure, and opportunity. Commitment means obligations carry through time. Consistency means stable patterns across people, cases, and cycles. Compassion means vulnerability is treated as real and harm as actionable. Connection means the person has standing, voice, and dignity. Contribution means participation creates mutual value rather than extraction.
The Trust anti-states are key because they explain why some evidence fails even when it is technically complete. A long document can create Confusion if it increases interpretive cost. A polished trust center can create Callousness if it ignores the human’s actual value exposure. A security claim can create Corruption if it relies on selective disclosure. A roadmap promise can create Abandonment if it lacks resourcing and follow-through. A support process can create Alienation if it resets the stakeholder to zero every time. The gate does not clear because the human did not experience safety: the artifact may be true in a narrow sense and still fail the affective surface required for permission.
The practical task is to define the target before creating the story. Who is the trust buyer? What exposure do they carry? Which gate are they operating? Which 8CM constituents must our trust stories activate for them to settle? Which artifacts can carry those constituents? How current must the proof remain? Which claim boundaries must be explicit? What revocation trigger applies if the underlying condition changes? This is the point where trust becomes engineering.
The Deli Counter and the Catapult
Sufficiency is contextual precision. Sufficiency-grade evidence is the smallest set of artifacts that makes a trust decision empirically and affectively acceptable to the exposed party. That definition has two parts. The evidence has to be empirically acceptable because the claim must be true, bounded, current, and tied to enforceable mechanisms. It also has to be affectively acceptable because the human at the gate must settle into permission. A fifty-document packet can fail if it does not answer the exposure. A three-page story can succeed if it binds the right claim to the right mechanism, lineage, boundary, and affective target.
“The enterprise buying process is a series of visits to the deli. Is this enough ham? It is about enough ham. All right, I will take it.”
The simplest analogy is the deli counter. The enterprise buying process often behaves like a series of visits to the deli. Is this enough ham? Eh, it’s about enough ham...all right, I will take it! That is a theory of threshold satisfaction. The buyer is not asking for infinite ham. They are asking whether the presented quantity and quality satisfy the purpose in front of them. Trust diligence works the same way. The trust buyer does not want infinite compliance evidence. They want enough of the right evidence to carry their exposure safely.
The “catapult of truth” teaches a different lesson. When a customer asks for a SOC 2 and a certificate of insurance, an ordinary company sends exactly those two things. A Trust Value organization understands that the request may be a surface expression of a deeper safety requirement. The “catapult of truth” was my name for sending a much larger, better-sequenced evidence package that communicated rigor, preparedness, and seriousness before the reviewer even opened a document. The affect hit before the cognition. The appearance of rigor, the weight of diligence, the feeling that this company had already done the work, all of that shaped the affective review field.
That mechanism is powerful and therefore dangerous. Artifact volume can create confidence, but it can also create noise. Documentation can be used to clarify or to overwhelm. Confusion is compatible with high documentation volume. A company can flood a stakeholder and call it transparency. TVM cannot degrade into that because Trust Quality exists precisely to prevent inert documentation and stakeholder flooding. The purpose is sufficiency, not weight. The catapult works only when the payload is true, certified, bounded, intelligible, current, and relevant to the gate. Without those governors, the same tactic becomes the manufacture of synthetic value safety.
A Trust Artifact is structured, validated, affectively resonant evidence intelligible to a trust buyer and capable of triggering a trust constituent. A policy, audit report, incident narrative, training record, monitoring dashboard, data flow map, postmortem, assurance packet, customer quote, or executive attestation can become a Trust Artifact only when it is prepared for gate use. It has to bind a bounded claim to a mechanism. It has to carry lineage. It has to have a validity window. It has to be revocable when conditions drift. Raw documentation becomes a trust artifact only after it can survive the gate.
Trust Quality is the certification discipline that makes this scalable. It owns admissibility, and asks whether the claim is publishable, whether the artifact activates the intended constituent, whether the evidence is stale, whether lineage is intact, whether the proof belongs inside a story, whether the claim is inside the claims registry, and whether revocation is defined. This is the conversion of legacy GRC posture into a value engine. GRC alone tends to produce documents. Trust Quality produces admissible proof objects that can be shipped into the field without local improvisation.
Marketing Throws Trust Stories Ahead
Once trust buyers are named and trust personas are installed, marketing changes. Everyone has a trust center that acts like a shelf. No one reads them until they are already anxious, already forced into diligence, or already trying to satisfy a buying process. In contrast, a Trust Story moves, travelling travels ahead of sales. It gives the hidden trust buyer a way to recognize safety before the formal gate closes around the deal.
“Everyone has a trust centre. No one reads them. What we need are stories.”
I sometimes describe this as “throwing a flag over the wall”. The old approach tries to batter through the wall by force. More calls. More pressure. More executive escalation. More discounts. More urgency. A trust story can cross the wall before that frontal assault on the account ever begins. If the flag gets raised on the other side, the sales team does not have to knock the wall down. It can go to the door and find someone already oriented toward value safety. That is the role of trust-buyer marketing: preparing the field before the trust buyer is asked to decide under pressure.
Customer success also changes. In the old model, customer success often tends the champion (and sometimes the economic) relationship. In a Trust Value model, customer success maintains the hidden trust buyer network behind the economic buyer. The CISO, counsel, integration lead, procurement operator, security reviewer, board-facing risk person, and legal stakeholder should not hear from the vendor only when a renewal review knocks at the gate. They should be kept inside a rhythm of safety: here is what changed, here is what improved, here is the new artifact, here is the updated story, here is the incident learning, here is the dashboard, here is the proof that you still do not have to worry about us.
When trust is built in, the account behaves differently. Audits become lighter. Renewal reviews become less defensive. Affiliates accept existing paper without re-litigating the relationship. Expansion becomes easier because the trust buyers behind the economic buyer already feel the organization is safe. Permission becomes cheaper. Diligence becomes less adversarial. Discounts become shallow. The customer stops treating the vendor as a recurring exposure event or liability surface.
This is not marketing trust into existence. You cannot market trust. Trust is an attractive force: you are pulled toward trust because the field feels safe, coherent, and worth approaching. Compliance pushes; it moves through coercion, obligation, process, fear, and penalty. A Trust Story works because it carries real evidence of real safe motion. Promotion can draw attention to that story. Promotion cannot substitute for the operating truth behind it.
Product, Engineering, and the Hidden Buyer
Product teams often believe they are disciplined because they cut away everything that is not essential to the user experience. That discipline has value but can become destructive when the product team defines the product world too narrowly. The person sitting in front of the interface is not the only person who determines whether the product can create value. The person who buys the widget may care about different things than the person who uses the widget. The person who permits the product into the enterprise may care about things the user never sees. If product ignores those people, product creates revenue friction while believing it is protecting focus.
“They are not going to be users of the product, but they are going to require first-class consideration as if they were.”
Trust personas gives product a lawful way to care about non-user requirements. They say: this person may never log in, but this person can block the sale. This person may never use the feature, but this person needs evidence generated by the system to pass a gate. This person may not care about the experience curve or the button color, but this person needs proof that data boundaries are clear, incident pathways are integrated, changes are governed, access is controlled, failure is contained, quality is measured, and commitments persist under pressure. These are product requirements because the product has to sell, renew, integrate, and survive adversarial scrutiny.
The pink dropdown feature does not sell anything if the gate cannot clear. Fixing the critical bug may sell something because it supports Competency, Consistency, and Commitment at a diligence gate. Building exportable access logs may sell something because it gives a CISO and auditor Clarity. Improving rollback paths may sell something because it demonstrates Error Containment. Building data lineage may sell something because it gives privacy counsel and legal a boundary they can trust. Product value is not limited to what delights the user in session. Product value includes what allows the exposure-bearing human to let the product into their system.
This is also how engineering gets out of the frantic iteration loop. Without trust personas, engineering receives trust-related work as late-stage escalation: a deal needs this control, a customer needs this report, legal needs this evidence, security needs this fix, procurement needs this answer. The team improvises, but the work fundamentally feels like interruption. With trust personas, recurring gate requirements become planned artifacts, product surfaces, data emissions, runbooks, dashboards, and story-ready outputs. The trust persona connects engineering work back to the Value Journey.
That connection is also how a security team gets budget. Security has spent years trying to justify work through risk language while the business runs on value language. Trust personas translate security work into value motion. A vulnerability fix can become a gate-clearing requirement. A monitoring capability can become sufficiency-grade evidence. A tabletop exercise can become a Trust Artifact. A postmortem can become a Character, Competency, and Commitment story. A control is no longer merely an internal control when it becomes a source of evidence yield. It helps the company make money by predictively lowering friction, accelerating permission, reducing concessions, and protecting valuation.
“Juan Carlos Makes Me Money”
The best way I know how to explain whole-business trust value is through Juan Carlos. When I was sixteen, my grandfather took me into one of his banks and asked me who the most important person in the bank was. I was sixteen, so I gave the obvious answer. Banks sell money, so the person who sells the most money must be the most important person. He pointed to Juan Carlos, the janitor, and told me that Juan Carlos was the most valuable employee in the bank.
“Juan Carlos makes me money.” -my grandfather
Juan Carlos remembered the customers’ names. He remembered which scent bothered Mrs. Garcia. He remembered the neighbor Mrs. Lopez brought in. He remembered the rituals and sensitivities that made the bank feel different from every other bank. My grandfather’s point was simple: every bank sells money. People think they choose the bank because of rates, safety, or service, but often choose his bank because Juan Carlos makes the place feel safe, known, stable, and human. Then my grandfather said the line that stayed with me: Juan Carlos makes me money.
That story revealed to me the difference between a businessperson and a playbook operator. A businessperson like my grandfather looks at every part of the business and asks how it can make money. The janitor, the training process, the hiring system, the support script, the incident response procedure, the DEI program, the policy register, the onboarding flow, the escalation path, the evidence library, the trust story, the customer advisory group, all of these can produce value if the business knows how to use them. If parts of your business exist that are not making money, either you do not know how to make them work, or you inherited a playbook that narrowed the definition of the productive business.
Trust Operations, Trust Quality, and Trust Culture formalize what Juan Carlos did intuitively. Trust Operations creates safe motion and evidence. Trust Quality converts raw evidence into admissible proof objects that ship to market while preventing bad claims, stale artifacts, inert documentation, and stakeholder flooding. Trust Culture keeps the business honest by shaping decision quality, language, accountability, and safe human motion. Together, they turn so-called cost centers into value-producing surfaces.
HR becomes a trust production surface. Hiring contributes to the trust product because who you hire affects whether stakeholders can trust the organization’s motion. Training is a trust product because decision quality depends on what people know, what they practice, and what they are expected to do under pressure. DEI is a trust product when it produces evidence of dignity, fairness, participation, and safety rather than symbolic theater. Safety is a trust product. Incident response is a trust product. Legal integrity is a trust product. Procurement posture is a trust product. The business makes more money when these surfaces generate evidence that trust buyers accept.
This is why the totalizing definition of ‘cost centre’ can itself become a trap. The company says sales and product are the business, while everything else supports the business. That frame leaves money on the floor. IT can make money if it emits evidence that clears gates. Security can make money if it lowers diligence friction and protects renewal. Legal can make money if it reduces negotiation drag while creating saleable paper. HR can make money if hiring, training, and culture create proof of safe human motion. Juan Carlos makes money because he changes the field in which customers decide. Trust Value Management turns that insight into an enterprise operating model.
Business or Vehicle
There is a strategic question that has to be asked early: is this business a business, or is this business a vehicle? The answer determines how TVM can be adopted. A business can learn to make more money with its whole company. A business can care about durable custody, stakeholder value safety, operating integrity, and trust production because it expects to live with the consequences of its decisions. A vehicle is different. A vehicle executes a financial motion designed elsewhere. Its operating model is compressed by the thesis that owns it.
“One of the strategic and highly difficult answers to get to is, is this business a business, or is this business a vehicle?”
This is a key structural distinction. In a fund-controlled environment, the thesis creates the simulation in which operators live. The metrics and the priority of those metrics become the walls of operating reality. The operator is often selected because they will run the playbook. They are not supposed to ask how the company could make money through every surface. They are supposed to execute the motion that advances the thesis and makes themselves manageable as a fund asset. The company may have real people, real customers, real products, and real value, but its governing logic may be vehicle logic.
TVM can still operate in vehicle contexts, but the sales motion changes. In a true business, the pitch can be whole-business value: make every part of the company produce trust value, lower friction, protect stakeholder value, and build durable advantage. In a vehicle, the pitch may need to be stabilization: your velocity thesis is fragile because trust friction will slow deals, increase concessions, expose valuation risk, and create unmodeled drag. TVM becomes the spoiler on a car being driven faster than its design should allow. It keeps the vehicle from lifting off the road.
The danger is that a vehicle may want the appearance of trust without the operating commitment. It may want the “catapult of truth” without Trust Quality, the trust story without safe human motion, or the trust premium without stakeholder value safety. That is why Trust Value Management requires bounded claims, evidence lineage, revocation, admissibility, and actual operating truth. A vehicle can buy outputs while resisting the obligations behind them. The trust value leader has to know which terrain they are entering to ensure ultimate outcomes for the organizations they serve
Trustable Certified Organic and the Human-Scale Company
The Trustable Certified Organic idea came from a simple recognition. Modern companies are replacing humans at such a clip that the customer cannot always tell whether they are dealing with a company made of people anymore. The interface may be automated. Support may be scripted. Decisions may be algorithmic. Responsibility may be dispersed. No one may be reachable. Everyone may be optimized out of the moment where the customer’s value is exposed. Under those conditions, human-scale governance becomes a market distinction.
“A company made of people, still serving people, governed by people at human scales.”
A Trustable Certified Organic™ company is made of people, still serving people, governed by people at human scales. The phrase sounds playful because it borrows the grammar of food certification, but the underlying claim is quite serious. The market increasingly needs a way to identify organizations that can demonstrate human custody of value, human accountability for decision quality, human-scale repair, human-readable evidence, and human governance over the systems that affect stakeholders. The Trustable Certified Organic™ company says: we still contain accountable human motion where your value is at risk.

This is not nostalgia for pre-automation business. Automation can be useful. AI can be useful. Software can be useful. The issue is whether the organization has preserved the human surfaces required for human-level trust to bind. Can a stakeholder get Clarity when the system acts? Can harm be treated with Compassion? Can constraints hold under incentive as Character? Can the system execute with Competency under load? Can obligations persist as Commitment? Can behavior remain stable as Consistency? Can people retain standing and voice as Connection? Can participation become mutual benefit as Contribution? If the company cannot answer those questions, automation has likely increased throughput while eroding trust value.
The Ethical Boundary
The machinery described in this essay has dual-use capacity. Affective engineering can create safety or simulate it. Stories can reveal truth or manipulate attention. Evidence can clarify or flood. Words can orient the human or push them into a field designed to bypass judgment. This is why the operating chain must remain intact as the foundation of the trust factory’s integrity. Safe human motion produces evidence. Trust Operations converts raw evidence into candidate artifacts. Trust Quality certifies admissibility, lineage, bounded claims, freshness, and revocation. Trust Stories compile certified artifacts for specific trust buyers at specific gates. 8CM defines the affective target vector. The trust buyer feels safe because the story corresponds to real custody performance and provable stakeholder value safety.
“Affective engineering can create safety or simulate it.”
That chain is the ethical governor. If a company skips safe human motion, the story becomes propaganda. If it skips Trust Operations, the artifact becomes unreliable. If it skips Trust Quality, the claim becomes uncontrolled and unbounded. If it skips revocation, the proof becomes stale. If it skips 8CM, the story may be correct but cold, or emotionally forceful in the wrong way. If it skips Stakeholder Value Safety, the whole system becomes a synthetic value safety factory.
Trust value leaders do not create the feeling of safety where safety does not exist. We do not use story to hide missing mechanisms. We do not use volume to bury the decisive fact. We do not ask a trust buyer to lean in beyond the evidence. We do not make claims outside the registry. We do not leave stale proof in the field. We do not treat the affective acceptance surface as a hack. Trust engineering is defensible because it binds affect to truth, truth to evidence, evidence to operations, and operations to stakeholder value safety, all. for the benefit of the value journey binding everyone together
Permission Becomes Cheaper When Safety Is Real
The lesson of trust buyers and trust personas is simple enough to carry. A trust buyer is a hidden customer at a gate. A trust persona is the internal planning object built from that customer. The Value Journey tells the business where the gates are. Trust friction tells the business where the map is wrong. 8CM tells the business what the human at the gate must feel. Trust Operations, Trust Quality, and Trust Stories turn real operations into proof that can move value safely.
“The real question at the gate is, is my value safest with you?”
Once you see this, the business reorganizes. Revenue stops treating diligence as an unpredictable swamp. Product stops treating trust requirements as interruptions from non-users. Security stops arguing from risk and starts producing investable value motion evidence. Legal becomes part of trust production rather than a late-stage defensive lane. Marketing stops storing trust and starts moving it. Customer success stops tending only the champion and begins maintaining the hidden trust buyer network. HR stops performing culture and starts producing evidence of safe human motion. Finance can see trust work as measurable value protection and acceleration.
The old question was, who has the budget and what pain do they feel? The better question is, which value is exposed, who carries the exposure, which gate must clear, what does that human need to feel, which proof will produce that settlement, and what operations must be true for the story to survive inspection? That question changes the company. It changes what product builds, what security measures, what marketing says, what customer success maintains, what legal permits, what HR produces, what finance funds, and what leadership understands as value.
Trust cannot be declared or marketed into existence. It cannot be audited into existence by frameworks alone. Trust is manufactured through safe human motion, converted into evidence, certified into artifacts, sequenced into stories, and received by humans who carry exposure at gates. When those humans feel safe enough to let value move, the business becomes faster, cheaper, more resilient, more attractive, and more valuable.
That is why everyone in the account is a customer. The person everyone calls a blocker may be the person carrying the most important question in the room. Is my value safest with you? If the answer is yes, and if the company can prove it in the form the gate can feel, value moves. If the answer is unclear, value slows, reprices, or stops. The work of Trust Value Management is to make the answer true, visible, felt, and governable before the gate becomes a crisis.



