Gatekeepers of Nothing
Why Cybersecurity Cannot Become What the Business Never Hired It to Be
The cybersecurity profession is built around a misunderstanding so old and so normalized that most people inside the field no longer perceive it as a misunderstanding at all. They experience it instead as frustration, as communication failure, as chronic underappreciation, as the endless necessity of translating cybersecurity into business language for an audience that never seems to hear it. An entire managerial literature has grown up around this irritation. Security leaders are told to become enablers, to think like the business, to speak in financial terms, to align with executive priorities, to avoid becoming the Department of No. The premise beneath all of this advice is that the cybersecurity profession and the business are fundamentally trying to do the same thing, but that cybersecurity has historically expressed itself badly. Fix the framing, fix the relationship. Learn the language of value, and the business will finally understand that cybersecurity is there to help.
That diagnosis is wrong. The persistent misalignment between cybersecurity and the business is not mainly a failure of rhetoric, temperament, or executive polish. It also persists because the role has almost never been given the machinery required to author outcomes in a language the business recognizes as its own. It is not cured by better slides, more mature dashboards, or a more commercially fluent CISO. The misalignment is older and more structural than that, the latest expression of an older managerial pattern in which expertise is invited into proximity with power, then contained there as advisory labor without authority over the terms by which the institution defines value, urgency, or reality. It begins with the fact that the business and the cybersecurity practitioner are not looking at the same object when they say the word “security.” They attend the same meeting, use the same vocabulary, and still mean different things. The business thinks it is directing one kind of function, while the practitioner believes they are performing another. Those two objects are not adjacent, only appearing adjacent because modern enterprise language has trained both sides to speak through euphemism.
The cybersecurity practitioner enters the profession through systems. Even when their route is distorted by credential factories, degree programs, or policy-heavy pathways, the legitimating mythology of the field still comes from the defender’s mental frame. Cybersecurity is presented as the work of understanding how complex systems fail, how they are traversed by adversaries, how trust boundaries are crossed, how software is abused, how identity is stolen, how persistence is established, how data is exfiltrated, how disruption is achieved. The field treats itself, at least in its self-description, as an adversarial craft. Its mythology remains built on terrain, exposure, and contest, even when its labor pipelines drift toward softer, more institutional forms of legibility.
A good cybersecurity person is supposed to know what is valuable, how it is exposed, how it can be attacked, and how to organize defenses proportionate to the seriousness of the threat. This is why so many practitioners, especially early in their careers, imagine themselves as guardians of something real. They believe they are being invited into a defensive role. They believe the business has something precious, knows it is precious, and is assembling an internal defense function around it.
That is almost never why the business hired them.
The business does not begin from the same ontology as the defender. It does not generally ask, with cold seriousness, what valuable object inside the enterprise must be protected at all costs, what internal army is required to defend it, what authority that army will need, and what degree of primacy it must be granted in order to preserve the value on which the enterprise depends. That is how a serious defensive organization would think. It would begin by identifying the thing whose compromise would materially wound the firm, then work backward from that object to create the protective structure required. But the ordinary business does not think in those terms. It does not think in value objects. It thinks in motion. More precisely, it thinks in temporal arbitrage.
The modern firm is organized around the movement of value through time. It wants to close, ship, scale, raise, acquire, expand, monetize, defer costs, accelerate exits, and compress delays between initiative and yield. Even when executives speak in strategic language, the underlying machine is temporal. It is also representational. Functions become strategically legible to it only when their outputs can be routed through planning, reporting, and attribution surfaces the enterprise already knows how to price. The firm increasingly perceives value through proxy surfaces it can price, report, circulate upward, and defend in audit form. It evaluates internal functions according to whether they accelerate or slow the conversion of present effort into future gain. This is why certain kinds of obstacles become visible to it and others remain obscure.
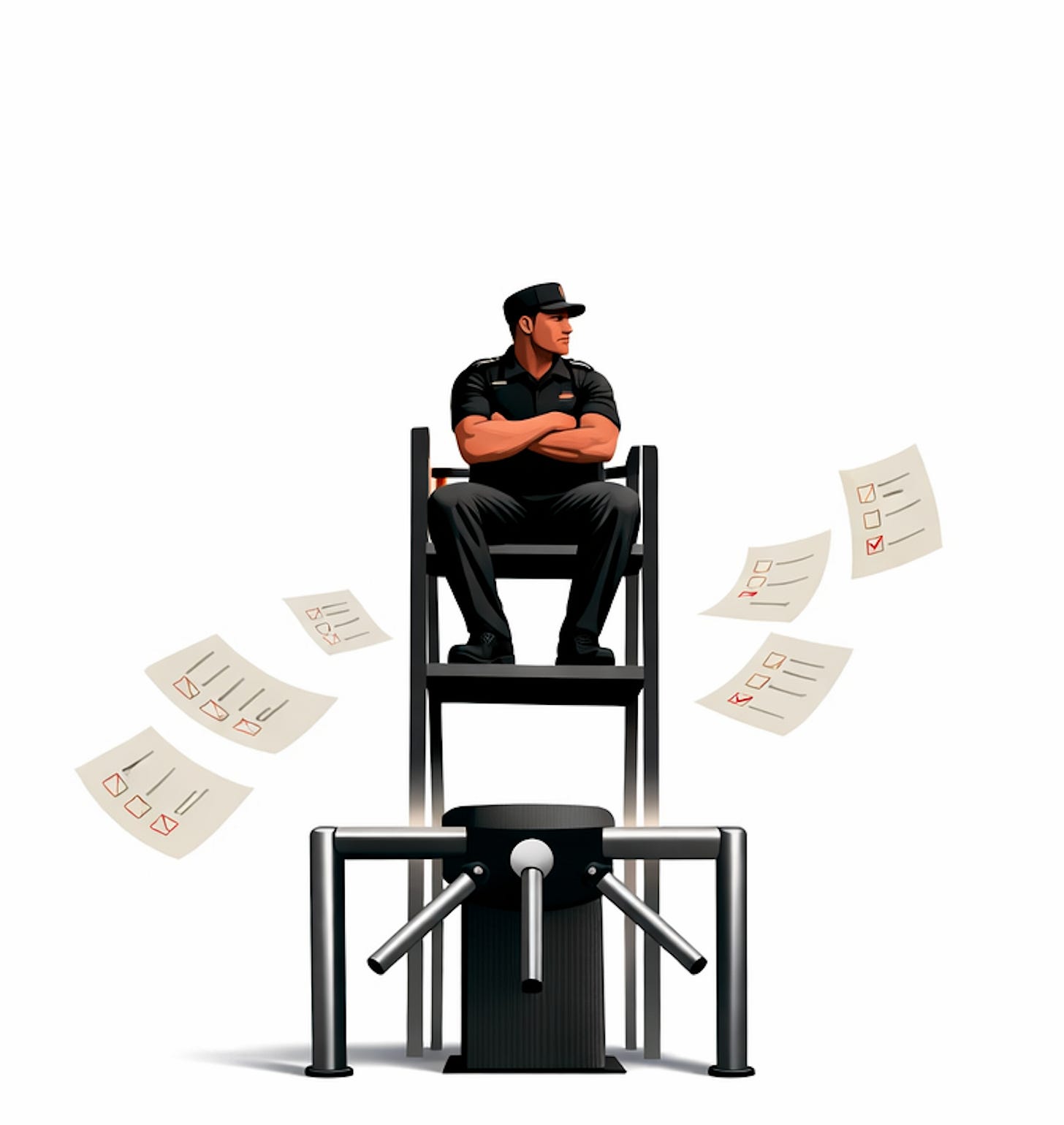
The business recognizes gates very clearly. It knows when something stands between itself and the value it wants to acquire. Procurement requirements, regulatory thresholds, customer diligence questionnaires, cyber insurance underwriting, audit conditions, investor scrutiny, contractual cybersecurity language, all of these appear as friction surfaces in the temporal path of value capture. The enterprise therefore hires specialists to deal with those surfaces. It also routinely under-models the full class of actors who can halt movement without ever owning a budget, which is one reason so much revenue drag appears inside the firm as mystery rather than structure. By the time cybersecurity appears in this chain, the business is often no longer looking at the defended object directly. It is looking at the evidence layer surrounding the object. It hires people who can satisfy the conditions required for motion to continue.
This is where cybersecurity enters the firm in practice. Not as an army assembled to defend the crown jewels, but as a gate management function required by counterparties, regulators, insurers, auditors, partners, and customers. The organization rarely says this aloud because it sounds crass and unserious, but that does not make it less true. In the ordinary company, cybersecurity exists because something outside the company demands evidence of control before money can move. Security is therefore funded and staffed as a permission function. It is measured less by preserved value than by cleared thresholds, sustained confidence, and successful passage through external checkpoints. It is one of the boxes standing between the business and the next state change it wants. The business experiences it as ordinary commercial reality. A deal requires a cybersecurity review. A customer requires a SOC 2 report. A regulator requires evidence of a policy being followed. An insurer requires MFA on all insured endpoints. A board requires assurance language for valuation. Hire the people who manage those requirements. Make the gate passable.
The entire tragedy of the cybersecurity profession begins here, because the cybersecurity practitioner almost never believes that this is the role they have entered. They believe they have joined the defenders, while the business believes it has hired the permission chaperones. One side thinks in adversarial defense of value objects, the other in transactional continuity. One side imagines a castle with vulnerabilities, valuable internal assets, and hostile external actors. The other imagines a sequence of commercial motions slowed by administrative conditions that must be satisfied. One side believes the job is to understand how complex systems are exploited and defended. The other believes the job is to ensure that the organization can continue moving through institutional and market checkpoints without unacceptable delay. They use the same title for both objects, then act surprised that the resulting relationship never stabilizes.
This explains a great deal that the profession otherwise misdescribes. Security leaders are constantly told to align with the business. They are told that they must become enablers, not blockers. They are told to think commercially, to understand revenue, to support the mission, to avoid absolutism. They are also told, often in the same breath, that they are responsible for protecting the enterprise from increasingly capable and relentless adversaries whose capacity to destroy your value exceeds your capacity to defend it. These messages are not merely in tension. They are the residue of two different managerial settlements layered on top of one another: the older expert-as-advisor settlement and the newer security-as-gate settlement.
They arise from different job theories. If you are actually the internal defense function for valuable enterprise assets under adversarial pressure, your posture, authority claims, escalation model, and formation logic should all reflect that seriousness. If you are primarily a gating function embedded in a temporal arbitrage machine, your success will be judged by how efficiently you reduce friction while preserving sufficient documentary credibility for external audiences. The profession spends a great deal of energy pretending that these are just two aspects of one harmonious role when they are actually rival interpretations of why the role exists.
Once this base misalignment is visible, many downstream absurdities become legible. Take the question of cybersecurity practitioner formation. Younger people ask how to get into cybersecurity and expect an answer shaped like an institution object. They want a degree, a certification ladder, an internship, a role title, some sequence that can be entered into the simulation and redeemed for placement. When you tell them to do all of IT first, to learn how large systems are actually built and where they break, to understand infrastructure, networks, operating systems, logging, applications, trust boundaries, operations, and only then to learn how to hack, they hear the advice as “unrealistic.” The reaction is revealing. It does not say the path is false. It says the path cannot be packaged cleanly enough for the institutional labor machine that now governs entry.
It does not engage the merits of the object. It does not ask whether this path produces stronger defenders. It simply rejects the advice because it does not compress into an institution-shaped route. Yet this advice is absolutely realistic in the only sense that should matter if the stated goal is competent defense of the value object. Cybersecurity is an adversarial craft. It sits on top of prior operational literacy. A defender who does not understand systems cannot reliably defend systems against people who do.
The training market resists this truth because the training market is not optimized to produce field-capable defenders. It is optimized to produce credentialed labor. Those are not the same thing. The market does not reward capability in raw form. It rewards capability once translated into signals the hiring and operating system can recognize, sort, and purchase. One produces workers who may survive contact with adversarial reality. The other produces workers who survive the hiring gauntlet. A university can sell a cybersecurity degree, a bootcamp can sell a cert bundle, a recruiter can search for the keywords, and HR can sort the resumes. None of that guarantees that the resulting worker can quickly identify exploits on a given network, stand up an SIEM stack, instrument a segment with an IDS sensor, interpret attack logs, test an application the way a criminal would, hunt for live threats, contain an active threat, or think adversarially about failure modes across a live environment.
Graduating with a degree in Cybersecurity and not being able to perform these tasks is not a failure on the part of the student: it is the credential production system speaking loudly. The credential certified institutional readiness, while the work demanded operational contact. The break between those two things is the entire indictment. The factory emits workers legible to the business because the business itself is not really buying adversarial value object defenders in the first place. It is buying institutional reassurance: it wants proof that it employed the right kinds of people, bought the right kinds of controls, adopted the right kinds of postures, and can therefore proceed through gates on its way to capturing value.
A labor market that actually centered defense against capable adversaries would form people very differently. It would force them through operational breadth, live system contact, technical friction, and adversarial testing. It would not assume that naming the domain is equivalent to knowing it. But that kind of formation takes time, exposure, failure, and real technical depth. It cannot be mass-produced cleanly. The industrial labor system therefore labels the hacker-craft path unrealistic and blesses the legibility path instead.
This is where many cybersecurity leaders go wrong in their diagnosis. They notice that the business undervalues real cybersecurity competence and overvalues presentational assurance. They correctly perceive that executives respond more readily to compliance objects than to deep technical warning about real value at risk. They see underprepared people being hired into roles they cannot actually perform. Then, they conclude that the solution is to make cybersecurity appear more business-friendly, more enabling, more aligned to growth. But this misses the deeper point. The business is not failing to recognize the true nobility of the function. It is recognizing the function according to the use for which it was purchased.
The business is not ignoring cybersecurity because its leaders failed to present it attractively enough. The business is receiving cybersecurity exactly through the optic that gave rise to the hiring decision in the first place. It did not hire a private army. It hired a friction manager for external confidence surfaces. That is why all attempts by cybersecurity leaders to help the business, enable the business, think like the business, and frame their work as business support are received only partially and always conditionally. The business is not waiting to discover that cybersecurity is a helpful partner. It already has a settled role concept for security, and that role concept is narrower than the practitioner’s self-understanding.
You can see the profession straining against this trap in the endless call for cybersecurity to “earn a seat at the table.” This phrase only makes sense if the speaker believes cybersecurity has not yet been properly understood by those who hold power over their function. If only the business could see the importance of security, if only the CISO could master the dialect of the boardroom, if only the function could demonstrate its support for revenue, then it would finally be granted primacy proportional to its importance. Thirty years of evidence say otherwise. The lock was visible long before most practitioners named it. The seat expands only when the enterprise needs the function to preserve motion, confidence, or market trust on terms it already accepts. That is not just the limit of the old role. It is also the clue to the successor lane.
Security receives as much table as the business’s underlying ontology of the role permits. Where cybersecurity is needed to close deals, it is tolerated and sometimes celebrated. Where cybersecurity can produce useful trust artifacts, it is valued instrumentally. Where cybersecurity threatens tempo, constrains motion, or insists on a defense-first posture not already ratified by commercial necessity, it is experienced as excess seriousness. This is not a temporary leadership problem. It is a stable reading of the function by the enterprise.
Law offers a useful comparison because it reveals the asymmetry more sharply. In legal work, everyone understands that there is an opposing party, an adversarial process, and a need to be sharper than the other side. No one seriously believes that one becomes a litigator by going to law school, learning the vocabulary of law, all while remaining operationally helpless in contested environments. The role is intelligible because contest is built into the business’s understanding of why legal counsel exists. Cybersecurity is different. The security practitioner experiences an adversary focused on obtaining the firm’s value. The business more often experiences the paperwork, procurement drag, customer scrutiny, and assurance burdens that the existence of adversaries generated.
Though the practitioner knows there is an adversary, the business often treats the role as if the adversary were secondary to the paperwork the adversary generated. It behaves as though the important part of cybersecurity is not the live contest with hostile actors, but the management of the institutional wrappers those contests created: the policies, audits, attestations, questionnaires, and compliance artifacts. In other words, it converts an adversarial craft into an administrative surface. That conversion is devastating to practitioner formation, role clarity, and authority.
The cybersecurity leader who tries to resolve this by “thinking like the business” steps into a trap. The phrase sounds mature because it suggests empathy, contextual intelligence, and executive fluency. But if the business is fundamentally not thinking in defended value objects, then thinking like the business means inheriting the business’s temporal arbitrage lens. It means seeing cybersecurity more and more as the management of friction around value movement, not as the organized defense of something precious. The more completely the cybersecurity leader succeeds at inhabiting that lens, the more they risk surrendering the substance of the craft in exchange for institutional approval. They become better at making cybersecurity legible to the enterprise precisely by reducing it to the form the enterprise is willing to recognize. This can produce local success, budget wins, smoother executive relationships, better narrative packaging. It can also turn the cybersecurity leader into a more elegant trusted advisor: closer to power, more legible to executives, and still structurally unable to redefine the role’s base ontology.
What it cannot do is cure the foundational contradiction, that it is not that cybersecurity leaders have failed to think like the business but that the business’s settled reason for having a cybersecurity function is not the same as the practitioner’s reason for being one.
This is why the role so often feels tragic to people who enter it seriously. They imagine they are joining the defenders and slowly discover that they are being measured as lubricants in a transactional machine. They think they are there to identify what matters most and construct defenses commensurate with the danger. The business asks instead whether the next audit will clear, whether the customer diligence packet is ready, whether procurement can proceed, whether the release can ship on time, whether the control language is sufficient to preserve momentum. The practitioner experiences this as a corruption of the role, the business as normal operations. Neither side is confused in a local sense: they are operating from incompatible base assumptions.
Once understood at this depth, the frustration sharpens. It is not chiefly frustration with weak practitioners, though weak practitioners abound. It is not chiefly frustration with bad training, though the training market is full of credential factories. It is not even chiefly frustration with executive ignorance, though executive ignorance is often real. The real content of the frustration is that the business does not know why it is hiring cybersecurity people in the way cybersecurity people believe they are being hired. The two paths do not eventually meet. They begin apart and remain apart. Security leaders can improve the interface, reduce some of the noise, create more useful trust artifacts, buy better local conditions, even deliver substantial enterprise value. None of that alters the base optic through which the firm reads the role. That optic is set by the business’s relation to value, time, proxy measurement, and external gating structures, not by the internal aspirations of the cybersecurity function.
This is the big reveal that many in the field spend entire careers refusing to name. There is no final alignment waiting at the end of better communication. There is no magical maturity level at which the business suddenly realizes that cybersecurity was really its internal defense force all along. There is no presentation style, no metrics framework, no executive storytelling technique that can make the enterprise spontaneously reconceive the role if the enterprise itself is not organized around defended value in the first place. The organization would first have to recover direct sight of what is valuable beneath the compliance layer, the reporting layer, and the transactional layer. Even that would not be enough. It would also need a way to bind that value, the stakeholders who can stall it, and the evidence that clears it onto the same executive surface. Most firms never begin there.
A real way out does exist, but it does not begin with better decks from cybersecurity leaders or greater moral enlightenment from the firm. It begins when the enterprise adopts a shared planning instrument that binds value objects, gate-owning stakeholders, evidence requirements, and commercial motion to the same operating surface. Under those conditions, the role stops appearing merely as a defensive overhead function and starts appearing as a system for preserving momentum, reducing hesitation, and protecting the future value embedded in the relationship. The key shift is architectural: what was previously framed as security work becomes legible as velocity stabilization, improved forecast accuracy, lower concession cost, stronger valuation defense, and more reliable capture of new value without sacrificing earned value already in hand.
This is the opening through which a different lane becomes possible. Once trust-critical gates, hidden veto actors, and evidentiary conversion are governed as part of the business’s actual operating system, the old role begins to give way to a successor form. At that point, the practitioner is no longer only a guardian speaking threat language into a tempo machine. They can arrive with a map of where value stalls, who has the authority to halt it, what proof restores motion, and how disciplined value defense improves go-to-market performance itself. This is the territory in which a trust-value operator, and eventually something closer to a Chief Trust Officer, becomes intelligible.
Businesses hire cybersecurity because something stands between them and what they want. Practitioners believe they were hired to defend what the business already has. Those are different functions born from different metaphysics. One is about passing gates. The other is about holding ground. All the pain in the profession radiates outward from that split.
That does not mean nothing useful can be done. It means the work must be named accurately. A cybersecurity leader can become highly effective at operating inside the split. They can understand when the enterprise needs trust artifacts, when it needs friction reduction, when actual hardening is possible, when theater is required, when truth is usable, and when seriousness exceeds the institution’s tolerance. They can build systems that create real defensive value even under a hiring ontology that does not fully acknowledge that value. They can sometimes smuggle substance in under the cover of assurance work, using the evidence layer to finance more serious contact with the defended terrain.
They can sometimes reprice cybersecurity in market-facing terms and route it through revenue logic. In the strongest cases, they can begin building the successor lane from inside the failing one, using trust artifacts, gate maps, and value-linked proof to teach the business a grammar it did not previously possess. But they cannot, by force of insight or goodwill alone, dissolve the underlying contradiction. The contradiction is upstream of them, present in the very reason the business agreed to fund the role.
So the profession’s endless advice to align with the business contains a hidden cruelty. It tells practitioners that the lack of stable acceptance is their own unfinished homework. That is the old trusted-advisor bargain restaged in cybersecurity form: become more fluent, more useful, more strategic, and perhaps power will finally concede what structure has already decided to withhold. It suggests that if they were a little less technical, a little more executive, a little more commercially literate, they would finally be seen for what they are. But what they are is exactly the question on which the two sides already disagree. The business is not withholding full recognition from a function it fundamentally understands. It is recognizing the function according to its own use for it. That use is narrower, more instrumental, and more temporally bounded than the practitioner’s self-concept. No amount of self-improvement by the practitioner can, on its own, reverse that fact.
The result is a permanent misalignment that is not accidental, not transitional, and not solved by professional development. Security people keep trying to be received as defenders but the business keeps receiving them as gate managers. The profession responds by producing more translation, more enablement rhetoric, more role softening, and more advice about empathy and executive framing. It keeps prescribing communicative improvement for an ontological fracture. Underneath it all, the original split remains intact. Until the enterprise itself begins from a value-defense ontology, until it identifies something precious and grants internal defense real primacy around that object, the cybersecurity practitioner will continue to live inside this contradiction. The role will remain haunted by two incompatible stories about why it exists. One story says cybersecurity is there to defend value under contest. The other says cybersecurity is there to render contested value legible enough for business motion to continue. And every earnest attempt to reconcile them through better behavior alone will fail for the same reason: the problem is not how cybersecurity leaders behave, but what the enterprise believes it bought when it hired them.